Adding the ability to repeat python command line arguments will provide a simple interface for content-based requesters. The graphical interface is equivalent to a transparent application. Constrained by a visual device or gadget along these lines of thinking.
Python command line arguments open up a tool that can catch and think your Python request is competing. Therefore, the practice of these characteristic area units will be adjusted according to changing strategies. For example, although your program may not currently perform real-time data checks in the records. Therefore, you can pass the report name to the timetable instead of hard-coding. So, the value into the American Standard Code for Information Interchange text archive.
Table of Contents
Through this method of the objective pursuit of practice, you may know:
Follow these principles and explain the premise behind python command line arguments
- Masking encourages python command line arguments
- Executive standards require interface game plans.
- In this way, retry and deal with the main points of Python request contention.
- Open the library with Python to encourage unnecessary work on requesting interfaces.
As it happens, I want to fight for the program’s Python request, not build an energetic library from a commercial perspective. Therefore, as it happens, I plan to discover more in the primary and general explanations behind most of the libraries for classification procedures. Python order interface, please continue to understand!
Request interface python command line arguments
In this way, the ordering interface (CLI) provides a way for the purchaser to move with the program running in the too complicated content-based shell negotiation program. Some shell intermediaries use Bash on the UNIX work framework work structure or use e-mail logging on Windows. Following these principles, the shell negotiation program approves the request interface, which looks for electronic communications. Following these lines of thought, the resulting components describe it:
- Request or procedure
- Zero ton or one ton requires competition.
- Demonstrate the speed of return once requested
- Therefore, the composed record is called the usage rate or support.
Not all request interfaces will provide these components. In any case, considering these things, this misfortune is not over yet, from the ability to pass the game, the required temperament, to the utterly unexpected feeling and decision. Based on the exact language of the site, this is comparable. For example, some requests will distribute network records from the right or start a reasonable shell intermediary program (Python) at the conspiracy level.
Two former models abused python command line arguments for an inheritance to depict the outline of an arrangement interface:
$ python-c “print(‘Real Python’)”
Real python command line arguments
In the basic model, the Python change program uses discrimination c to speak to the order. It executes the Pythopython order contention request competition as a Python program about choosing c.
Another model shows the easiest to use thanks -h for Python to offer help:
- $ python-h
- Use: python3 [option]…[-c cmd | -m mod | record| -] [arg]…
- Options and arguments (and consider setting factors):
- -b: issue warnings about str (bytes_instance), str (bytearray_instance)
- Also, use str to control byte/byte clustering. (-Bb: disadvantage error)
- […The general support text does not appear…]
- Try to enter your terminal to determine the total comfort file.
C’s legacy python command line arguments
Python request competition is obtained directly from the C pseudo-language. As Guido Van Rossum wrote for Unix/C developers in 1993, he wrote the necessary complicity degree of Python, C influenced Python. Guido determines which method to use for words, identifiers, heads, and pronunciation (for example, interrupt, continue, or return). Also, the use of Python request competition will even be tortured by the C language.
- To describe the comparability, consider the C program created:
- /main.c
- #include
- int primary (int argc, sear * argv []) for (int I = 0; I 0
- }
The fourth line describes the quality of Principle (), which can be part of the program inspiration. Reasonable consideration limit:
argc is the classification of the degree of collaboration and the degree of program competition.
argv is a brief reminder of the collusion level, which contains the program name’s characters, encapsulated in the display’s essential part. The caterpillars are followed by program contention (assuming any idea), and these contentions are placed in the remainder of the party.
You can take advantage of GCC-o’s essential main objects. c Redo higher code than the UNIX working framework. Now, if it is not very troublesome, please use ./guideline to prompt the associated code:
$ GCC -o main.c python command line arguments
- $ ./Basic
- Serious reminder: one
- Competition 0: ./Basic
Unless you explicitly convey -o through decisions and commands, a.out is the default name for works created by the GCC compiler. It involves the production of PC programs and is similar to the actual records made on the more mature UNIX work framework. Therefore, please note that work name/.essential is an exclusive competition.
We should encourage this model to bypass various Python request conflicts to comparable projects:
- $ ./Standard Python request boundary
- Competition check: 5
- Conflict 0: ./ rule
- Argument 1: Python
- Contest 2: Command
- Competition three: good
- Argument 4: Argument
The pace of earnings indicates a level of competition of five. Therefore, the reduction in evaluation includes the program’s name, which is pronounced immediately after each “Python request Arguments” passed inside the order.
Note: argc stands for competition check, and argv stands for competition vector. To find a large number of substances, you can choose to provide suggestions in the C Primer / C request argument.
Therefore, the Principle of development. C expects you to use only the UNIX working framework or waterproof shell OS structure. On Windows, you might use everything related to ensuring results that are coordinated:
UNIX Windows Framework (WSL): There are very few UNIX working frameworks, such as Ubuntu, OpenSUSE, and Debian. You can show it from the Microsoft Store.
Windows Era Tools: It contains a Windows request transfer device, Microsoft C/C++ compiler cl.exe, and C/C++ compiler named clang.exe.
Microsoft Visual Studio: This can often become Microsoft’s most useful improvement tool (IDE). Go back and view a large amount of data about a day, such as Windows. It will be used for each Python and C in various dynamic structures. For example, Windows. In addition to learning about Python one day, you can also learn about code proofreaders (direct ).
Mingw-64 Enterprise:
This supports the GCC compiler on Windows.
If you have already set it in Microsoft Visual Studio or Windows Build Tools, you want to make the necessary settings. C is as follows:
- C:/> cl main.c
- You will get a conspiracy job called main.exe. Starting from the following code:
- C:/>Main
- Serious reminder: one
- Argument 0: Principle
You can execute the Python program main.py, for example, the program main.c you saw earlier:
#Main.py
Import framework python command line arguments
Occasionally __name__ == “__main__”:
Print (f “All limits:”)
In my case, arg in the count (sys. argv):
Print (f “competition:”)
You will not see the concomitant degree argc variable as in the C code model. Because of the system. argv is sufficient. It does not exist in Python. You can give up the Python group competition in sys. argv. You can’t deal with the time reduction anyway. Even if the program needs to read in real-time, you can choose to set lens.
Similarly, if there is not much trouble, please note that once distinct() is applied to associativity and iterability, it will return the companion list object, generating the part of the input sys. Arginine of the same value as a companion. This may emphasize the essence of sys while at the same time not tending to record the counter in the blueprint.
Execute main.py as follows:
- $ python main.py Python request boundary
- Competition statistics: 5
- Conflict 0: main.py
- Argument 1: Python
- Contest 2: Command
- Competition three: good
- Argument 4: Argument
The system Args contains comparable information based on the C program:
So, the name of the program main.py is the premise of the framework.
Also, the competition for Python, Command, Line, and Arguments forms part of the blueprint.
A brief introduction to the dark areas of the C language. In this way, you will choose to obtain a handle to some primary data to accept any Python request competition.
Two utilities within the scope of the UNIX work framework bundle
Use Python to ask questions in this objective tracking exercise. Following these lines of thought. You can perform most of the decisions of the following. Two utilities within the regular system of the UNIX work framework work structure:
So, you will get some contradictory data about the operational structure of the UNIX working framework.
sha1sum can measure the SHA-1 hash value. So, it has been changed according to the super-large degree to check the accuracy of the report. For a given data, the hash work will permanently restore the fuzzy value. In this way, any fragile changes within the information may result in an unscalable hash value. Before using a utility with strict restrictions, you can try to help:
- $ sha1sum-help
- Use: sha1sum [option]…[file]…
- Similarly, or check SHA1 (160 pieces) check.
- Regardless of whether there is no FILE, or once FILE is -, please check the standard data.
- -b,-double-check
- -c,-always check the SHA1 set in the record and prevent them
- -Confirm name age BSD fashion
- In this way, the text can be checked in a generous mode (default)
- Therefore, the zero results of each result line is NUL instead of newline,
Also, keep the favorite titles moving.
[…There is no utterly exciting content]
So, the presentation requester’s help can also be the average component displayed in the solicitation interface along these lines.
To calculate the SHA-1 hash value of the record content, please proceed as follows:
$ sha1sum main.c
Therefore, the result shows the SHA-1 hash value, the basic field. Likewise, in this methodology, the recorded name maintains the fact of the following space. Therefore, the request can agree to some kind of conflict:
$ sha1sum main.c main.py
Consider the advanced functions of the UNIX working system terminal. In this way, it can create contention for Python requests with unusual condition characters. One such name is a pointer or indicator (*):
$ sha1sum fundamentals. *
3f6d5274d6317d580e2ffc1bf52beee0d94bf078 main.c
f41259ea5835446536d2e71e566075c1c1bfc111 main.py
Python order contention faq
How to pass boundary in python command line?
To use the getopt module, you want to process the basic part of the order boundary list.
Language structure: getopt.getopt (a
RGS, alternatives, [long_options])
boundary:
args: The reduction of the boundary to be passed.
Alternative: A line of decision letters that the content can perceive.
How to use report routing as a restriction in Python?
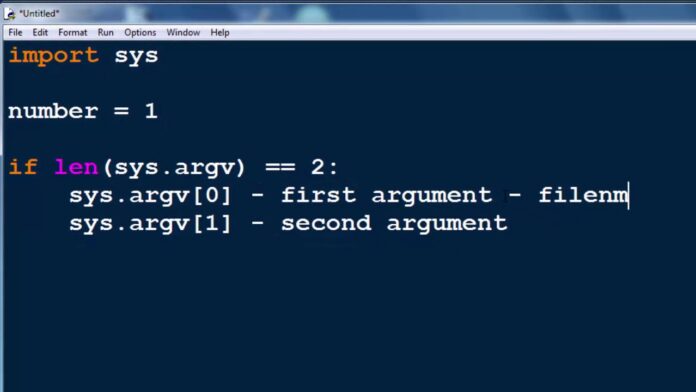
To pass the record name from pummel to Python, use sys. argv [1] Record the name starting from the restriction: use open (sys.argv [1],’r’) as in_file to import sys. At that time, you will have the option to use different A restrictions, which will use various restrictions. So, these restrictions may be things, factors (same or completely surprising information types) and restrictions.
How to pass request limit while Python sleeps?
1) Although it is of great significance. So, you can still choose to clearly determine the “necessary” work on the IDLE console. 2) Therefore, you can choose to add a research line. Before the most call to convey a limit value (or produce a unit test close to the limit) or set sys. argv directly.
How to run request limits?
In order to pass the request limit, we will use two limits to draw major() roughly. So, the basic limit is a combination of request limits. Also, the second limit may be a worldwide request limit. Therefore, the estimate of argc should be a non-negative grouping. argv (ARGument vector). According to these principles. So, it is a variety of character pointers used to issue all restrictions.